BLOGDOG
Your personal cyber security and anti-hacking news
Exploit Kit: What It Is and How To Protect Yourself
The term ‘exploit kit’ may not be a popular among everyday consumers and Internet users, but that doesn’t mean it shouldn’t be. This is especially true considering how security concerns have become more widespread lately, especially after the numerous major data breaches of 2014 that affected millions of people.
Exploit kits are powerful tools that allow hackers to steal personal information from a vast number of victims all at once. An exploit kit contains a group of exploits, or pieces of code that were written with the purpose of taking advantage of (or exploiting) a vulnerability on a victim’s machine and running malicious code on it. An exploit kit can live in any website a hacker was able to inject it into. They are perhaps the most heinous of the various tools hackers have in their arsenal. Part of this is because of the fact that, with exploit kits, a hacker can infect the computer of an everyday Internet user without the user even downloading or running anything—and quickly infect that user’s machine with malware such as a Trojan horse, or, worse yet, make the victim’s computer part of a large network of machines capable of doing things like taking down websites.
And don’t go thinking that exploit kits only live in shady websites. Hackers are breaking into legitimate websites in order to inject exploit kit code into them. They even have automated tools that crawl the Internet for them, testing the security of websites in search of holes that can allow them to inject exploit kits into the site.
That’s the short version of the exploit kit story. The more detailed version that allows us to really understand the entire story behind exploit kits is a bit more complex—and worth knowing about!
The Angler Exploit Kit (credit: TheHackerNews.com)
The Nitty Gritty About Exploit Kits
First, let’s start with the fact that there are a variety of exploit kits out there. Some of these include the Angler exploit kit, the Blackhole exploit kit and the RIG exploit kit—and they can all do different things.
But how does the everyday Internet user even come in contact with or get their machine infected by an exploit kit? This happens by a method of infection called a drive-by-download, and an opportunity on the user’s machine called a vulnerability.
A vulnerability—whether it’s in your operating system (i.e., Windows), your browser (i.e., Chrome), or any other application you have (Adobe, Word, etc.)—is what allows malicious code (or malware) to run on your computer. Part of what exploit kits do is poke and prod your machine in the attempt to discover vulnerabilities that can be exploited in order to infect your computer with malware.
A drive-by-download is the infection method that enables an exploit kit to infect your computer without you doing anything beyond merely browsing to the infected website. By visiting a website that points to an exploit kit (i.e., a website someone has hacked and injected the exploit kit into) and having a vulnerability on your computer that one of the exploits in the kit can exploit, your machine can get infected. This is called a “drive-by-download,” and it greatly contributes to the exceptional sizes some botnets reach these days. If drive-by-downloads seem scary, that’s because they are! Unfortunately, not only are drive-by-downloads rather sophisticated, they’re also very common.
Botnets?
Wait, botnets? What are those? A botnet is a group of malware-infected machines. Botnets are extremely powerful; they can steal information, send massive amounts of emails as part of a spam campaign, and even take down the most resilient of websites. And they can get big. Botnets can grow to include hundreds of thousands, and even millions of infected machines.
So now we know that we can get infected by malware by simply visiting a website that has been hacked and having a vulnerability on our machine that the exploit kit buried in the hacked website can exploit. Now let’s take a deeper look into exploit kits from the hacker’s perspective.
The Hacker’s Exploit Kit
With what we’ve already discussed here about exploit kits, it’s pretty easy to imagine how and why they have become so popular within hacker circles. Evident to that is the amount of exploit kit versions that exist out there: the Blackhole exploit kit, Phoenix exploit kit, Redkit exploit kit and Styx exploit kit, just to name a few of the exploit kits that have been observed by security companies (there are likely many others that haven’t yet been discovered).
Some of these exploit kits are sold in the underground economy. Others are so widely available that they are literally given away for free. And others still are “private,” used exclusively by the cybercrime gangs who developed them. Some exploit kits are an evolution of previous versions, containing code of older exploit kits. One example is the Lightsout exploit kit, which reuses code that was seen in the Dragonfly exploit kit. All of this contributes to the notion that there is an explosion of exploit kits out there. If this hacking tool wasn’t working well, exploit kits wouldn’t be as popular as they are today.
From the hacker’s perspective, there are two main ways of employing exploit kits. The first one involves hacking into a legitimate website and injecting it with code that brings up the exploit kit. This means that the hacker is changing the website’s code so that it calls the exploit kit every time someone visits the site. In fact, one of the most straight-forward ways Internet users’ machines get infected by exploit kits is by simply running JavaScript, which most everyday users do (without even knowing it, sometimes). JavaScript is computer code that browsers know how to run, and they open up a world of possibilities to web developers. As such, JavaScript is what makes a lot of websites fun. But JavaScript also opens up a world of opportunities for cybercriminals, since exploit kits are written in JavaScript. So, if JavaScript is running on your browser, exploit kits can affect your computer.
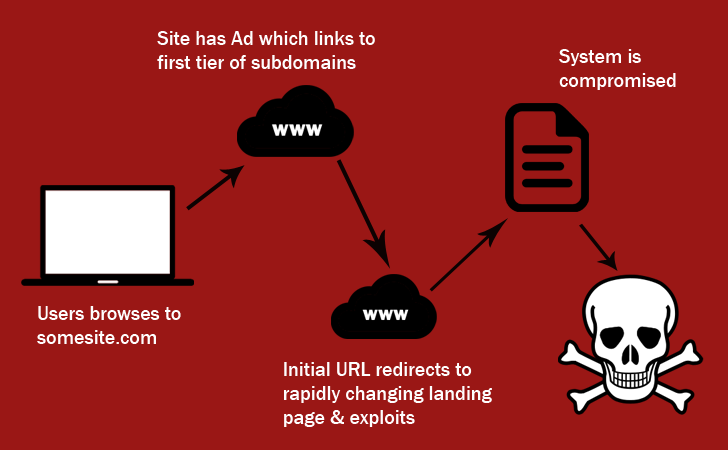
The second method of getting people to communicate with exploit kits is by a hacker building a unique page for them. This could be a page that looks like an ad for a fake product, or a page for anything else, really. The truth is that it doesn’t matter what the page is for; the idea is to merely attract visitors and infect their machines with malware. Once such a page is built, it’s up to the hacker to drive traffic to the site. One very interesting method hackers use to do so is called Malvertising. Malvertising uses ad networks such as Google Ad Words to place ads in legitimate sites. But malvertising ads advertise fake products, and if you click on them, you’ll be directed to hackers’ malware-serving pages.
Malvertising is a major issue, especially because it works so well. By providing huge exposure to malware-infected pages, and generating so many visitors to those pages, cybercriminals are able to infect a large number of machines within a relatively short time. Unfortunately, while advertising networks do try to stop malvertising, their attempts aren’t always successful.
There are many exploit kits that have been found to use malvertising as a method of promoting their malware-serving pages. Some examples are the Angler exploit kit, the super popular Blackhole exploit kit and the RIG exploit kit.
What You Can Do To Avoid Becoming an Exploit Kit Victim
You didn’t think we were going to dump all that bad news on you and run, did you? Fortunately, there are some steps you can take to avoid being a victim of an exploit kit. Here’s what we suggest:
- Always keep your computer updated. You should never hold off on applying patches and fixes, since they may contain security fixes to the exact vulnerabilities that exploit kits try to exploit.
- Use an antivirus software. Some of the modern antiviruses these days do more than just scan your hard drive for any known threats. Some of them also scan the websites you surf to, identify any evidence of the site being hacked and, if found, stop the page from loading. In fact, it’s best to specifically choose an antivirus software that offers this feature. If you need help finding the right antivirus, out these recommendations for the Best Free PC Antivirus Software.
- Use NoScript (if you’re really paranoid). NoScript is a Firefox add-on that prevents JavaScript from running on your browser. If JavaScript can’t run on your browser, exploit kits can’t affect your computer regardless of what vulnerabilities your machine may contain. But bear in mind: NoScript can be a bit of a hassle until you tell it in which sites to block JavaScript (and the more sites you allow, the more you open yourself to the possibility of getting infected). If you’re a Chrome user, you can use a NoScript alternative such as ScriptSafe.
- Go Mac or Linux. It’s true, moving to a whole new operating system can be daunting. But, next time you find yourself shopping for a new computer, you may want to consider the security implications of your choice. Mac’s operating system is no less vulnerable than Windows, but because it has a smaller market share, chances are that cybercriminals would prefer focusing on Windows.
Did you enjoy this post? If so, subscribe to get a weekly roundup from BlogDOG.
About LogDog
The LogDog anti-hacking and privacy tool protects the most popular online account types including Gmail, Facebook, and Dropbox by detecting unusual access activity and alerting users so they can take control of their accounts before hackers do.











